$ 0.126 1.12%
Neblio (NEBL) Rank 1478
The Neblio Platform wants to provide fully open source APIs, tools, and services needed by business and enterprises to rapidly develop and deploy distributed applications. Replacing legacy database applications with truly scalable and reliable distributed applications through the development of familiar and easy to use API abstraction layers is the goal of the Neblio Platform.
| Mkt.Cap | $ 2.64 M | Volume 24H | 0.00000000NEBL |
| Market share | 0% | Total Supply | 13 MNEBL |
| Proof type | Open | $ 0.12 | |
| Low | $ 0.12 | High | $ 0.13 |
Neblio
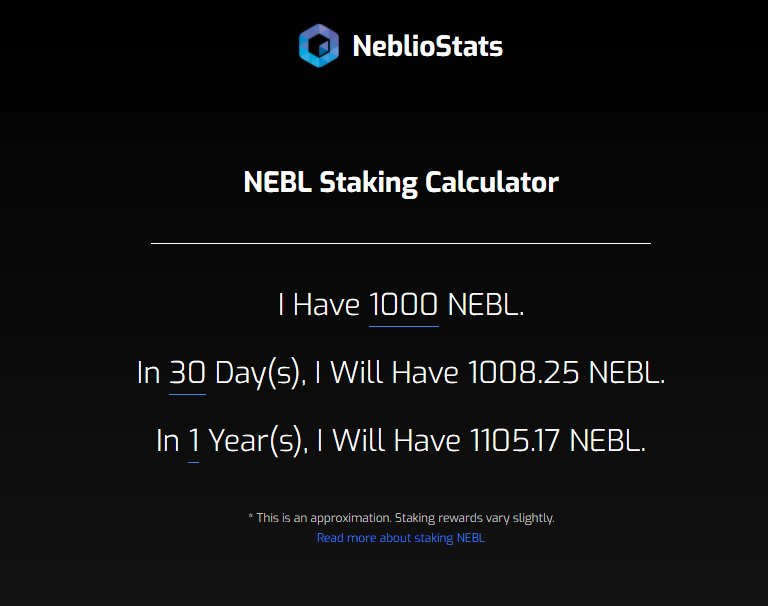
The Neblio Network uses a Proof-of-Stake algorithm where users stake NEBL coins to secure the network. To encourage staking and securing the network, the network rewards users for the time spent staking. The network is set to generate new coins at a rate that is variable depending on the number of coins currently being staked on the network at any given time. Vulnerabilities relating to this repository, the core software running the Neblio Network, are eligible for this program. Out-of-scope vulnerabilities impacting other software we release may be considered under this program at Neblio's discretion.
Such a block would only be found invalid if it was part of the best chain and was about to be connected. Final part of the validation in the block connection process would reveal that the used coins were already spent. In order to fix this denial of service vulnerability, Neblio implemented additional validation checks inside of VerifyInputsUnspent. Nebbiolo planted in Novara and Vercelli region of northern Piedmont tend to produce lighter and earthier wines.

Neblio (NEBL) is a cryptographic token that operates on its own blockchain, facilitating fast transactions of 120 seconds. Early in AcceptBlock, it calls VerifyInputsUnspent function, which is a new function implemented by Neblio in response to fake stake vulnerability. This vulnerability allowed an attacker to use already spent coins for creation of seemingly valid coinstake transaction and thus seemingly valid block.
Outside Piedmont, it is found in the neighboring regions of the Val d'Aosta region of Donnaz and Valtellina and Franciacorta in Lombardy. In the Veneto, there is a small amount which some producers use to make a Nebbiolo recioto wine. Nebbiolo is thought to derive its name from the Italian nebbia or Piedmontese nebia, meaning "fog". During harvest, which generally takes place late in October, a deep, intense fog sets into the Langhe region where many Nebbiolo vineyards are located. As they age, the wines take on a characteristic brick-orange hue at the rim of the glass and mature to reveal other aromas and flavors such as violets, tar, wild herbs, cherries, raspberries, truffles, tobacco, and prunes.
Neblio (NEBL) - description and review of cryptocurrencies
Nebbiolo wines can require years of aging to balance the tannins with other characteristics. Neblio in operation, it resembles a blockchain network like many other cryptocurrencies, such as Bitcoin. So it is a distributed register based on a network of nodes (nodes or masternodes) that communicate in the form of so-called transactions.

Outside Italy, producers in the United States are experimenting with plantings totalling 68 hectares (170 acres) in California, Washington, Oregon and even Virginia. In the Northern Region of Baja California, Mexico, 180 hectares (440 acres) support the production of the Nebbiolo varietal.
Eventually the difficulty will decrease enough for the attacker to produce a chain that looks healthy and it is fully controlled by the attacker. This allows the attacker to perform additional attacks such as double spending.
In the whitepaper team clearly stated that the tokens are not in any way "shares" or any other form of investment, i.e. nobody will take them for securities (securities). In the future, the possibility to adapt the Neblio API to work also on other blockbinding networks not based on Neblio - this is therefore an element of flexibility in the developers' approach to the project.
In 2010, there were 5,536 hectares (13,680 acres) of Nebbiolo producing 125,000 hectolitres (2,700,000 imp gal; 3,300,000 US gal) of wine which accounted for a little over 3% of Piedmont's entire production. In contrast, there is nearly 15 times as much Barbera planted in the region.
Neblio Team

Nebbiolo has a long history in the Alba region of Piedmont. In this scenario the attacker targets one or more specific nodes that the attacker wants to disable.

This will cause that all the block propagation in the network will only have to go through the public nodes of the attacker. This allows the attacker to censor any transaction as well as censor any block, which further allows the attacker to create a longest chain with just fractional stake, compared to the original staking power of the network. With just fraction of the network staking power, the difficulty will go down very quickly because the blocks will not be produced within the expected timeframe.


- What if there is a catastrophe and we will not have access to the patient file that is in our hospital?
- The Neblio Token Protocol-1 and its unique metadata properties allow for easy tokenization of physical and digital assets without any development or technical experience.
- This allows the attacker to perform additional attacks such as double spending.
- In the Northern Region of Baja California, Mexico, 180 hectares (440 acres) support the production of the Nebbiolo varietal.
- In this scenario, the attacker buys nontrivial amount of coins and it also performs a sybil attack against the network – this means it will create a large number of fully operational public nodes.
- whitepaper Neblio tokens to be used to create, distribute and use dapps.
bugs which can incur Denial of Service (DoS) in the Neblio network through the RPC-API. bugs which can incur Denial of Service (DoS) in the Neblio network through P2P network. bugs which can lead to unauthorised transfer or generation of coins/NTP1 tokens. This Bug Bounty program is an open offer to external individuals to receive compensation for reporting Neblio bugs, specifically related to security of the core functionality of the network.
Such a block would then cause VerifyInputsUnspent to load all blocks in the blockchain to the memory from the database. At the time of writing there are more than 750k blocks in the Neblio main chain.
Blockchain.Simplified.
Nebbiolo is also grown in smaller amounts in South Africa, Uruguay and Chile. A secure, distributed, platform built for enterprise applications and services. We design and develop open-source products and services to drive business value from the Neblio blockchain network. Companies will require to use Neblio to make transactions on the Neblio blockchains. So the more transactions that they'll make the more Neblio that they'll need (or will need to stake).
But, to my knowledge running a new NTP1 costs pack of chewing gums. The Neblio Platform aims to provide fully open-source APIs, tools, and services for enterprises to deploy dApps.

The attacker needs a direct connection to the target node, so we expect the target node to be operating on publicly accessible network interface – i.e. public IP address and open firewall port. Eventually, the attacker is able to create connection to every public node in the network and disable all such nodes. would be nice to have a description on the github page and if you don't want to clutter that page, a descriiption of how to set up and use the nebliod on the blog. So, if for example I create new NTP1 token for my business, would that require that I buy certain amount of NEBL, or I just rely on NEBL holders to hold and secure and run the platform.

Which will increase the demand for the coin and the price will raise. I have invested in Neblio, and I like the project altogether. I'm thinking whether to add some more but it is very difficult for me to estimate value of the NEBL coin.
In this scenario, the attacker buys nontrivial amount of coins and it also performs a sybil attack against the network – this means it will create a large number of fully operational public nodes. Then it will perform scenario one attack against all other public nodes in order to disable them.

Neblio Price Index, Historical Chart and Market Cap
They enable saving data in a blockchain network through specially created applications. Recording and reading of data takes place via the API, each data manipulation must be confirmed by the network and therefore application data has an additional high level of protection against unauthorized access.

The ability to create individually selected and / or private blockchain networks based on the Neblio network. Operators verify transactions, provide governance, and create new blocks. Staking NEBL is as easy as leaving your wallet running and connected to the network.
Today, many projects and programs in IT are based on shared solutions. Migrations or changing the programming environment should not be a problem.
Modern RESTful API architecturewhose future development is to be flexible and based on feedback from programmers. The intention is to be an absolute simplification of the API on the users' side so that the developers on the client's side can prepare Dapps without even knowing about the operation of the blockchain network. The Neblio Network is lightning fast today and ready to scale with the future.
In each of these nodes there is a copy of the transaction book in the form of the so-called blocks. Each new transaction is broadcast by the network, so that the nodes are able to compare and check the compliance of such a new transaction. Projects using decentralized network applications such as Neblio go a step further and instead of saving dry transactions in the blockchain, they allow for more.
Because most of the blocks are empty, the whole chain is quite small, so this approach would cause problems with memory only for nodes running on very restricted hardware. However, loading so many blocks from disk and processing them takes a lot of time. We have tested exploitation of this bug with the target node running on a dedicated low-end machine. Thus we expect that processing such blocks can take between 2 to 10 minutes depending on the hardware the node is running on.