$ 0.000 0.65%
Simple Token (OST) Rank 2185
| Mkt.Cap | $ 206,470.00 | Volume 24H | 112.17 MOST |
| Market share | 0% | Total Supply | 800 MOST |
| Proof type | N/A | Open | $ 0.0003 |
| Low | $ 0.0002 | High | $ 0.0003 |
Basic Attention Token

User tokens allow you to work directly on behalf of users, based on the OAuth scopes they award to your app. user User tokens allow you to work directly on behalf of users, based on the OAuth scopes they award to your app. Bot user tokens let your app act independently. Previously, bot users were special and required the umbrella bot scope. New Slack apps can request individual scopes for their bot users, just like with user tokens.
It’s important to remember that fees need to be paid for all token transactions on a blockchain, not just the creation of the token. Therefore, any application built on Ethereum must use Ether coins to transfer the application- specific tokens from one user to another or between the app and the user.
Token Based Authentication Made Easy
▪Client Timeout This is the timeout value used to determine how long the firewall should wait until it considers the SecurID server unreachable. ▪Client Retries This is the number of times the firewall (SecurID Client) will try to connect to the SecurID server. Although access to this list is secured with the additional factor of the banking card and its PIN code, this can be regarded as another example of paper-based strong authentication. The login page that is shown randomly selects a password to be entered. The user has a laminated piece of paper with these passwords, which is used to find the requested password.
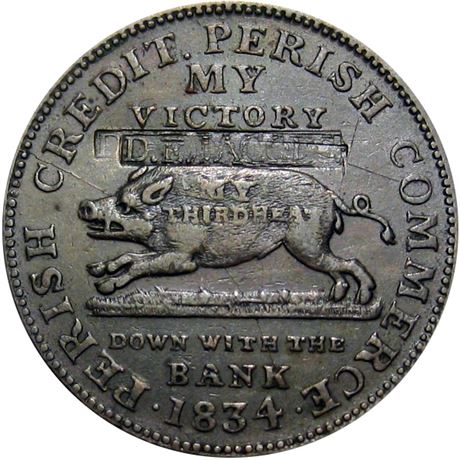
Coins are most often used simply as money; however, some coins do have other uses. These include being used to fuel applications, being used as a stake to validate a transaction on a network, or being used to fuel smart contract and token transactions.
In order for the SecurID server to be able to authenticate, the user must be given the token's serial number, which is mapped to a particular user and the seed number for the batch. Lastly, the token is synced up with SecurID server, and you now have two-factor authentication. When the user logs in, they present their username and password, which is appended with the number on the keyfab.

There are some disadvantages which will invariably come along with security tokens. Removal of middlemen leads to the shifting of responsibilities onto the buyer or the seller in the transaction.

For example, a typical OpenID Connect compliant web application will go through the /oauth/authorize endpoint using the authorization code flow. The signature is used to verify the message wasn't changed along the way, and, in the case of tokens signed with a private key, it can also verify that the sender of the JWT is who it says it is. Although JWTs can be encrypted to also provide secrecy between parties, we will focus on signed tokens.

Protocols Built on OAuth 2.0
The crypto community breath a sigh of relief when SEC has ruled Bitcoin and Ethereum to not be securities. As of right now, security tokens have a far less share of the market as compared to utility tokens, however, security tokens are something which can become huge in 2018 and needs to be embraced by everyone soon. It is believed that tons of capital is going to flow from Wall Street to security tokens instead of utility tokens.
This also protects user privacy and helps shield a member company’s inner metrics of its application to the outside world, while being open and accountable with their branded tokens. They are issued for the user who installed the app and for users who authenticate the app. When your app asks for OAuth scopes, they are applied to user tokens. You can use these tokens to take actions on behalf of users.
A platform for performing the role of token service provider as defined by EMVCo to tokenize primary account (PAN) numbers. It handles the entire lifecycle management of issued tokens and stores the mapping with the original card number in a secure token vault. These not only include tokenizing payment cards for e-commerce and mobile payments (HCE and OEM Pay wallets) but also bank account numbers for ACH/real-time payments, as well as cryptocurrency wallets. Visa offers standards, specifications, development tools, and turnkey mobile solutions to help partners build and deploy their own tokenized apps to cardholders. This shift is happening because security tokens are considered to be safer because of the strict regulations.
You can even use the Google Pay API to offer one-touch checkout experiences for hundreds of millions of Google users and request any credit or debit card stored in your customer’s Google Account. A Google Pay user adds a credit or debit card to their Google Pay app. Google Pay requests a token to represent the card they’re trying to add from the bank that issued that card. Once the token is issued, this card is now “tokenized,” meaning it has a unique identification number associated with it. Google Pay encrypts the newly tokenized card and it is ready to be used for payments.

This feat is accomplished by the use of a hardware token whose number changes every minute. Each number is chosen by a proprietary algorithm that uses the hardware serial number, and the unique seed file sent with each batch of tokens to determine what the number is at any given moment.
- There are some disadvantages which will invariably come along with security tokens.
- The Brave browser knows where users spend their time, making it the perfect tool to calculate and reward publishers with BATs.
- It will remain in our system until you withdraw your consent.

When users trade with BNB (Binance token), their fees are 50% less. Once created, tokens are often used to activate features of the application they were designed for. In fact, thanks to the creation and facilitation of smart contracts, the most common blockchain token platform are Ethereum.
Casper is deployed on the Simple Token network as well. As OST spans out over many utility chains with all value staked on Ethereum, all work to strengthen and scale Ethereum greatly benefits the ecosystem, and as a result OST. They take on the full operational scope of the user that created them. If you're building a tool for your own team, we encourage creating an internal integration with only the scopes it needs to work.
OST News & Events
However, JWT and SAML tokens can use a public/private key pair in the form of a X.509 certificate for signing. Signing XML with XML Digital Signature without introducing obscure security holes is very difficult when compared to the simplicity of signing JSON. Let's talk about the benefits of JSON Web Tokens (JWT) when compared to Simple Web Tokens (SWT) and Security Assertion Markup Language Tokens (SAML). Do note that with signed tokens, all the information contained within the token is exposed to users or other parties, even though they are unable to change it. This means you should not put secret information within the token.
When first implemented, Hadoop frameworks were notoriously bad at performing authentication of users and services. This allows users to impersonate as a user the cluster services themselves. You can be authenticated to the Hadoop framework using Kerberos, which can be used with HDFS access tokens to authenticate to the name node. Kerberos is a secure method for authenticating a request for a service in a network. Kerberos was developed in the Athena Project at the Massachusetts Institute of Technology (MIT).
The enrollment process, which is different from MOTP, is server to client, and in most cases it is based on a QR code with manual entry in case the device does not have a camera. In addition to authentication, the tokens can be used to sign a ConfigMap. This is used early in a cluster bootstrap process before the client trusts the API server. The signed ConfigMap can be authenticated by the shared token.
When the contract acknowledges that this transaction is done, they receive their corresponding amount of tokens. Since everything on Ethereum is decentralized, an ICO is considered a success if it is properly well-distributed and a majority of its chunk is not owned by one entity. Firstly, the developer issues a limited amount of tokens. By keeping a limited amount of tokens they are ensuring that the tokens itself have a value and the ICO has a goal to aim for.
These tokens simply provide users with a product and/or service. For tokens to identify the user, all tokens must have some kind of number that is unique. Trusted as a regular hand-written signature, the digital signature must be made with a private key known only to the person authorized to make the signature. Some use a special purpose interface (e.g. the crypto ignition key deployed by the United States National Security Agency). Cell phones and PDAs can also serve as security tokens with proper programming.
Breaking Down Simple Agreement for Future Tokens (SAFT)
CoinSwitch aggregates rates across cryptocurrency exchanges all at one place, allowing users to pick and choose the most favorable rates for them. No requests are made on behalf of users with workspace tokens.

Another type of one-time password uses a complex mathematical algorithm, such as a hash chain, to generate a series of one-time passwords from a secret shared key. Each password is unguessable, even when previous passwords are known. The open source OAuth algorithm is standardized; other algorithms are covered by US patents.
OAuth 2.0 focuses on client developer simplicity while providing specific authorization flows for web applications, desktop applications, mobile phones, and living room devices. This specification and its extensions are being developed within the IETF OAuth Working Group. If you want to read more about JSON Web Tokens and even start using them to perform authentication in your own applications, browse to the JSON Web Token landing page at Auth0. Security-wise, SWT can only be symmetrically signed by a shared secret using the HMAC algorithm.

A common example of a two-factor authentication is when one uses his or her ATM card and has to enter a PIN. Some organizations not only require a username and password to authenticate to the VPN, but also give employees a token with a random set of numbers that change every 30 seconds.
A utility class for representing a token in the Simple API. This nominally tries to conform to a CoreLabel-like interface, though many of the methods are not supported (most notably, the setters). Regarding usage, JWT is used at Internet scale. This highlights the ease of client-side processing of the JSON Web token on multiple platforms, especially mobile. JSON parsers are common in most programming languages because they map directly to objects.