$ 0.663 -5.03%
Quantum Resistant Ledger (QRL) Rank 589
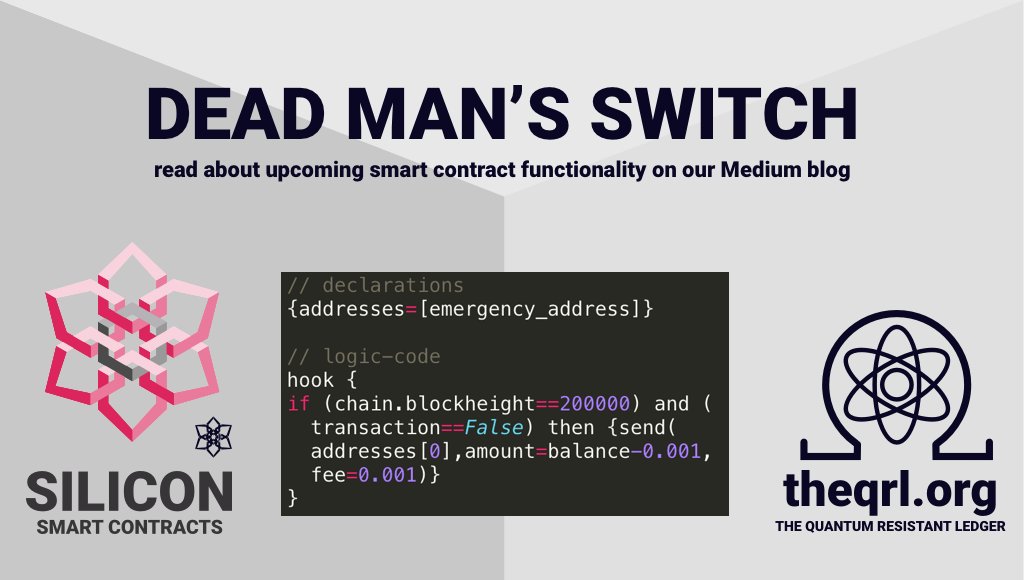
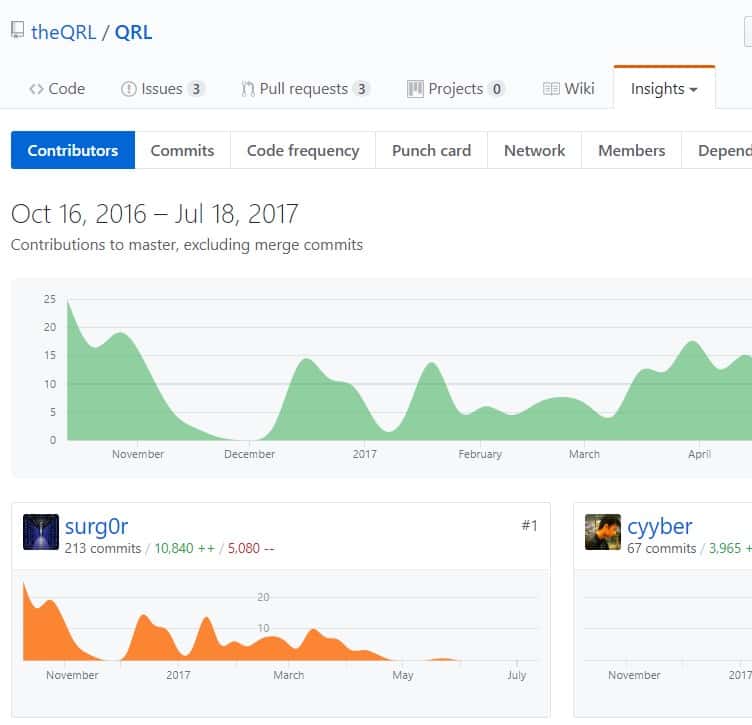
QRL is a Python-based blockchain ledger utilising hash-based one-time merkle tree signature scheme (XMSS) instead of ECDSA. Proof-of-stake block selection via HMAC_DRBG PRF and a signed iterative hash chain reveal scheme. It was designed to resist potential quantum computer hacks.
| Mkt.Cap | $ 52.37 M | Volume 24H | 117,005.00QRL |
| Market share | 0% | Total Supply | 65 MQRL |
| Proof type | PoS | Open | $ 0.70 |
| Low | $ 0.64 | High | $ 0.72 |
No, Google and Its Quantum Computer Aren't Killing Bitcoin Anytime Soon
Since a more computationally intensive hard problem means a stronger cryptographic system, it follows that elliptic curve cryptosystems are harder to break than RSA and Diffie-Hellman. The key characteristic of RSA algorithm is that is contains one process that is easy to do but difficult to undo.

Quantum Resistant Ledger is a cryptocurrency based on the Python programming language, aimed at combating future attacks by quantum computers.
How does ECC encryption work?
Elliptic Curve Cryptography or ECC is a public key cryptography which uses properties of an elliptic curve over a finite field for encryption. For example, 256-bit ECC public key provides comparable security to a 3072-bit RSA public key.
The easy part of the algorithm multiplies two prime numbers, while the difficult pair is factoring the product of the multiplication into its two component primes. Algorithms that have this characteristic are known as Trapdoor Functions. Finding a good Trapdoor Function is critical to making a secure public key cryptographic system. Simply talking, the bigger the spread between the difficulty of going one direction in a Trapdoor Function and going the other, the more secure a cryptographic system based on it will be. There are numerous symmetric algorithms, but most enterprises use the Advanced Encryption Standard (AES), published in 2001 by the National Institute of Standards and Technology after five years of testing.
Lattice-based Cryptography – NTRU encryption
Tim Hollebeek, industry and standards technical strategist at DigiCert points out that unlike classical computers, quantum computers are best at solving certain very specialized problems. However, for those problems, they are far better than classical computers ever will be. Examples include simulating other quantum mechanical processes, solving complex interconnected equations for weather prediction or artificial intelligence, and factoring very large numbers. Blockchain is first and foremost a public (or sometimes private or hybrid) database that is open and decentralized. Open means anyone can read it unconditionally, and anyone can write into it after meeting certain conditions.
Standards bodies are actively evaluating PKC systems from these families, looking for efficient algorithms with no known vulnerabilities to either classical or quantum attacks. IEEE and ANSI's X9 Committee have already specified standards for quantum-safe PKC schemes. ETSI and NIST have both issued reports on post-quantum cryptography, and NIST is currently evaluating 69 proposed schemes for U.S. government use. To quantify the security of cryptosystems, "bits of security" are used. You can think of this as a function of the number of steps needed to crack a system by the most efficient attack.
How fast is a qubit?
A 30-qubit quantum computer would equal the processing power of a conventional computer that could run at 10 teraflops (trillions of floating-point operations per second). Today's typical desktop computers run at speeds measured in gigaflops (billions of floating-point operations per second).
This means that the compromise of one message cannot lead to the compromise of others, and also that there is not a single secret value which can lead to the compromise of multiple messages. This is viewed as a means of preventing mass surveillance by intelligence agencies. This includes cryptographic systems such as the Rainbow (Unbalanced Oil and Vinegar) scheme which is based on the difficulty of solving systems of multivariate equations. Various attempts to build secure multivariate equation encryption schemes have failed. However, multivariate signature schemes like Rainbow could provide the basis for a quantum secure digital signature.[17] There is a patent on the Rainbow Signature Scheme.

It replaced the Data Encryption Standard (DES), which debuted in 1976 and uses a 56-bit key. Either way, the worries that quantum computers will soon break Bitcoin, blockchain, the internet and everything else worth loving in the world may be overheated, at least in the short-term. The news is not all bad; there are efforts afoot to find the next crypto-algorithm that will stand up against quantum computers should they become reality.
The idea is simple — if computers can compute fast, make the puzzle more complex. Their idea is to create a blockchain using quantum particles that are entangled in time. That would allow a single quantum particle to encode the history of all its predecessors in a way that cannot be hacked without destroying it. Registered, or buffered, memory is not the same as ECC; the technologies perform different functions. It is usual for memory used in servers to be both registered, to allow many memory modules to be used without electrical problems, and ECC, for data integrity.
ETSI Quantum-Safe Cryptography (QSC) working group

It's like a mailbox — anyone can stick letters in through the front slot, but one needs the (private) key to open up the back and take anything out of it. “The security of a blockchain is guaranteed by its cryptographic functions, and the most common one in the industry is at risk in the face of quantum computing. Additionally, unlike centralized systems, decentralized systems need the active consent and participation of all users to achieve something like total address type migration, which is what would be necessary to achieve quantum resistance,” he said. When large-scale universal quantum computers are built, you will still be able to securely use symmetric encryption algorithms, but not the systems like RSA and Diffie-Hellman. These PKC systems are widely used today to create digital signatures or to securely transmit symmetric encryption keys.
- Variations of the "break any contemporary encryption" prediction are the most common—and the most terrifying.
- However, the time to produce alternatives for existing encryption algorithms may be now.
- Recently, a paper by computer scientists published in Nature magazine even goes so far as to suggest that blockchain could be made obsolete by quantum computing.
- It takes many years to invent a new encryption algorithm, many years to test it in competitions or in real-world programs, and many years still to see it deployed in most applications.
- Symmetric encryption requires that the sender and receiver both use the same algorithm and the same encryption key.
- With the advancement of mathematics and computational power, the gap between the difficulty of factoring large numbers and multiplying large numbers is shrinking, hence the size of the keys need to grow even faster.
How long does it take to be a hacker?
Most people who try can obtain a decent skill set in eighteen months to two years if they completely concentrate on it. However, hacking is a vast ocean which takes years to explore its mystery. And if you are a genuine hacker, you will spend the rest of your life learning and developing your craft.
In 1994, years before the first experimental quantum computers existed, Peter Shor published an algorithm that can efficiently break numbers down into their prime factors. This contrasts with important encryption and key-exchange algorithms like RSA and Diffie-Hellman, which are vulnerable. Recently, I gave a little talk at ISE about quantum computing; I tried to delve into the subject a little deeper than what you might receive from a popular magazine or web news outlet. Following my talk, the ISE team jumped into a deeper discussion, questioning if an algorithm that is deemed "quantum resistant" is really safe. After all, with some celebrated exceptions (think one-time pad), no cryptographic algorithm can be totally resistant to cryptanalysis—even in the conventional sense.
Monero is very vulnerable, but so is Bitcoin. Hard to be quantum resistant when we don't know what powers the Quantum computing era will have.

Hash-based cryptography
This problem can be mitigated by using DRAM modules that include extra memory bits and memory controllers that exploit these bits. These extra bits are used to record parity or to use an error-correcting code (ECC). Parity allows the detection of all single-bit errors (actually, any odd number of wrong bits).
This weakness is addressed by various technologies, including IBM's Chipkill, Sun Microsystems' Extended ECC, Hewlett Packard's Chipspare, and Intel's Single Device Data Correction (SDDC). An ECC-capable memory controller can detect and correct errors of a single bit per 64-bit "word" (the unit of bus transfer), and detect (but not correct) errors of two bits per 64-bit word. Elliptic curve cryptography (ECC) is a public key encryption technique based on elliptic curve theory that can be used to create faster, smaller, and more efficient cryptographic keys. ECC generates keys through the properties of the elliptic curve equation instead of the traditional method of generation as the product of very large prime numbers. Besides creating longer RSA keys, users are also turning to elliptic curve (EC) algorithms, based on the math used to describe curves, with security again increasing with the size of the key.

How long would it take to crack 512 bit encryption?
The cost and time required to break 512-bit RSA encryption keys has plummeted to an all-time low of just $75 and four hours using a recently published recipe that even computing novices can follow.
ETSI QSC ISG seeked to standardize the relevant algorithms, primitives, and risk management practices as needed to seamlessly preserve our global information security infrastructure. Quantum-safe cryptography refers to efforts to identify algorithms that are resistant to attacks by both classical and quantum computers, to keep information assets secure even after a large-scale quantum computer has been built. When such a question is asked about a coin, it's about the crypto behind keys and signatures. Monero uses standard ECC (elliptic curve crypto - just like Bitcoin and 99% of coins) and as such is vulnerable.
Quantum Computing and the risk to security and privacy
Does quantum computing destroy Bitcoins?
Although cryptographic hash functions, such as the SHA-256 used in Bitcoin, are quantum computer reliable, the Secp256k1 encryption method, like all ECDSA algorithms is vulnerable to quantum computers. A powerful quantum computer will be able to destroy Bitcoin with its current technology.
This line that 'we don't know what quantum computers can do' really doesn't fly when choosing to pick algorithms that are known to be quantum-insecure. There are quantum resistant signature schemes, but currently they usually need both huge keys and generate huge signatures (tens of kilobytes both).

He is focused on enabling operating efficiency and deriving business value through the optimization and control of technology. Mr. Finn’s key skills include IT Governance and Control, Project Management, Systems Selection and Implementation, Business and IT Partnering, and IT Audit, Control and Security. Dr. Ponemon has held chaired (tenured) faculty positions and published numerous articles and learned books. He has presented hundreds of keynote speeches or learned presentations at national or international conferences on privacy, data protection, information security, corporate governance, and responsible information management. Dr. Ponemon is an active member of the International Association of Privacy Professionals, serving as founding member of the Certified Information Privacy Professional (CIPP) Advisory Board.
For example, a quantum computer can calculate the private key from a signature, but that does not help it since there is no longer any credit on the address. Mr. Finn has more than 30 years’ experience in the planning, management and control of information technology and business processes.