$ 0.001 6.58%
Data Transaction Token (XD) Rank 4894
| Mkt.Cap | $ 0.00000000 | Volume 24H | 0.00000000XD |
| Market share | 0% | Total Supply | 1000 MXD |
| Proof type | N/A | Open | $ 0.0006 |
| Low | $ 0.0006 | High | $ 0.0006 |
Tokenization
Data Transaction Token is a decentralized cryptocurrency thats ranked #1195 by market cap. Data Transaction Token has a maximum supply of 1000M XD and a circulating supply of 198M XD. XD is down by -0.81% in the last 24 hours with a volume of ?. For more information about Data Transaction Token, check out their websites scroll.network, twitter or explorers etherscan.io, ethplorer.io and forums medium.com, telegram. Vaultless tokenization and stateless tokenization have been independently validated[18] to provide significant limitation of applicable PCI Data Security Standard (PCI DSS) controls to reduce scope of assessments.

Tokenization (data security)
The website provides a list of cryptocurrency and bloclchain related events, valid and authentic list of cryptocurrency wallets and Bitcoin mining pools. We also provide rich advertisement campaings to advertise your bussiness on this website. LVTs also act as surrogates for actual PANs in payment transactions, however they serve a different purpose.
The infeasibility of reversing a token or set of tokens to a live sensitive data must be established using industry accepted measurements and proofs by appropriate experts independent of the service or solution provider. When properly validated and with appropriate independent assessment, Tokenization can render it more difficult for attackers to gain access to sensitive data outside of the tokenization system or service.
The Network Value to Transactions (NVT) ratio calculates the dollar value of crypto transaction activity relative to the network value. CoinGecko provides a fundamental analysis of the crypto market. In addition to tracking price, volume and market capitalization, CoinGecko tracks community growth, open-source code development, major events and on-chain metrics.
Data Transaction Token

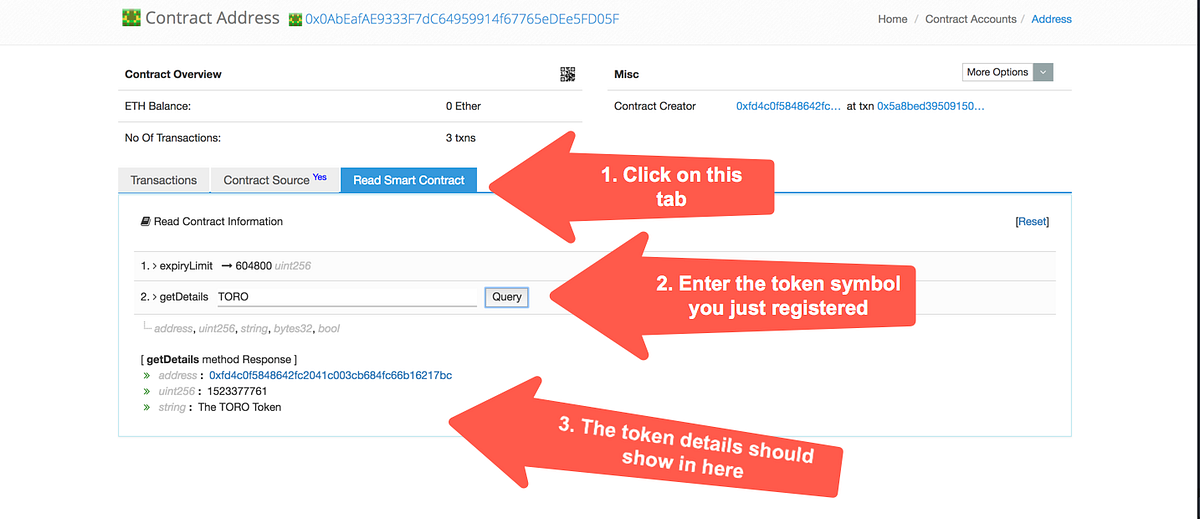
The digital asset, Data Transaction Token, is used to initiate private data transactions by users onto the public Ethereum Blockchain, rendering each transaction immutable. "Voltage Secure Stateless Tokenization Advances Data Security for Enterprises, Merchants and Payment Processors".
HVTs serve as surrogates for actual PANs in payment transactions and are used as an instrument for completing a payment transaction. Multiple HVTs can map back to a single PAN and a single physical credit card without the owner being aware of it. The Data Transaction Token token is now trading at 0.04x in USD and 0.13x in ETH from the ICO price.
Significant consistency, availability and performance trade-offs, per the CAP theorem, are unavoidable with this approach. This overhead adds complexity to real-time transaction processing to avoid data loss and to assure data integrity across data centers, and also limits scale. Storing all sensitive data in one service creates an attractive target for attack and compromise, and introduces privacy and legal risk in the aggregation of data Internet privacy, particularly in the EU. Tokenization is a non-mathematical approach that replaces sensitive data with non-sensitive substitutes without altering the type or length of data. This is an important distinction from encryption because changes in data length and type can render information unreadable in intermediate systems such as databases.
Bitcoin’s price increased after Jack Dorsey’s announcement

Applications can operate using tokens instead of live data, with the exception of a small number of trusted applications explicitly permitted to detokenize when strictly necessary for an approved business purpose. Tokenization systems may be operated in-house within a secure isolated segment of the data center, or as a service from a secure service provider.
As a security best practice,[27] independent assessment and validation of any technologies used for data protection, including tokenization, must be in place to establish the security and strength of the method and implementation before any claims of privacy compliance, regulatory compliance, and data security can be made. This validation is particularly important in tokenization, as the tokens are shared externally in general use and thus exposed in high risk, low trust environments.
- The Data Transaction Token token is now trading at 0.04x in USD and 0.13x in ETH from the ICO price.
- This requires the storage, management, and continuous backup for every new transaction added to the token database to avoid data loss.
- The token is a reference (i.e. identifier) that maps back to the sensitive data through a tokenization system.
- Visa Inc. released Visa Tokenization Best Practices[24] for tokenization uses in credit and debit card handling applications and services.
LVTs cannot be used by themselves to complete a payment transaction. In order for an LVT to function, it must be possible to match it back to the actual PAN it represents, albeit only in a tightly controlled fashion. Using tokens to protect PANs becomes ineffectual if a tokenization system is breached, therefore securing the tokenization system itself is extremely important. This is a simplified example of how mobile payment tokenization commonly works via a mobile phone application with a credit card.[1][2] Methods other than fingerprint scanning or PIN-numbers can be used at a payment terminal. No crypto news related to XD found, if you're aware of anything related to Data Transaction Token, please let us know.
1 Bitcoin = 4896968 Data Transaction Token (XD)
Instant Crypto Credit Lines™ from only 5.9% APR - unlock your crypto-wealth tax-efficiently, without selling it. Earn up to 8% interest per year on your Stablecoins, USD, EUR & GBP.
Tokenized data is secure yet it can still be processed by legacy systems which makes tokenization more flexible than classic encryption. When tokens replace live data in systems, the result is minimized exposure of sensitive data to those applications, stores, people and processes, reducing risk of compromise or accidental exposure and unauthorized access to sensitive data.
It fuels the movement of data change records from a company’s semi-private ledger to a public blockchain and represents value to the validator facilitating that action. Trading and investing in digital assets is highly speculative and comes with many risks.
This allows tokenized data to be processed more quickly and reduces the strain on system resources. This can be a key advantage in systems that rely on high performance.
Implementation of tokenization may simplify the requirements of the PCI DSS, as systems that no longer store or process sensitive data may have a reduction of applicable controls required by the PCI DSS guidelines. Another difference is that tokens require significantly less computational resources to process. With tokenization, specific data is kept fully or partially visible for processing and analytics while sensitive information is kept hidden.

Difference between Apple Airdrop & Crypto Airdrop

The analysis / stats on CoinCheckup.com are for informational purposes and should not be considered investment advice. Statements and financial information on CoinCheckup.com should not be construed as an endorsement or recommendation to buy, sell or hold. Please do your own research on all of your investments carefully. Scores are based on common sense Formulas that we personally use to analyse crypto coins & tokens. Past performance is not necessarily indicative of future results.
TrustCommerce developed TC Citadel®, where customers could reference a token in place of card holder data and TrustCommerce would process a payment on the Merchants behalf.[8] This secure billing application allows clients to safely and securely process recurring payments without the need to store cardholder payment information. Tokenization replaces the Primary Account Number (PAN) with secure, randomly generated tokens. If intercepted, the data contains no cardholder information, rendering it useless to hackers. The Primary Account Number (PAN) cannot be retrieved even if the token and the systems it resides on are compromised nor can the token be reverse engineered to arrive at the PAN. Tokenization may be used to safeguard sensitive data involving, for example, bank accounts, financial statements, medical records, criminal records, driver's licenses, loan applications, stock trades, voter registrations, and other types of personally identifiable information (PII).

Tokenization as a security strategy lies in the ability to replace a real card number with a surrogate (target removal) and the subsequent limitations placed on the surrogate card number (risk reduction). If the surrogate value can be used in an unlimited fashion or even in a broadly applicable manner as with Apple Pay, the token value gains as much value as the real credit card number. In these cases, the token may be secured by a second dynamic token that is unique for each transaction and also associated to a specific payment card. Example of dynamic, transaction-specific tokens include cryptograms used in the EMV specification.